How to Keep Your Data Private
An article published yesterday by Reuters casts a shadow on Apple’s commitment on privacy and encryption.
When Apple spoke privately to the FBI about its work on phone security the following year, the end-to-end encryption plan had been dropped, according to the six sources. Reuters could not determine why exactly Apple dropped the plan.
“Legal killed it, for reasons you can imagine,” another former Apple employee said he was told, without any specific mention of why the plan was dropped or if the FBI was a factor in the decision. (…) However, a former Apple employee said it was possible the encryption project was dropped for other reasons, such as concern that more customers would find themselves locked out of their data more often.
Like, e.g., Daring Fireball’s John Gruber, we firmly believe that Apple has absolutely no interest in your and our data. They’re selling hardware, not advertising. For whatever reason exactly, it seems that while the backups iOS devices upload to iCloud are encrypted, it’s not an end-to-end encryption and Apple also has a key. Depending on the laws in your country, agencies could ask them to hand over your data over without you knowing.
We have always believed that your data should be yours, and yours alone. Our applications don’t collect any data they don’t need for functioning. They also never share your data with anyone unless you tell them to do so. Our privacy policy has more on this and we’ve published a few more articles on privacy here on our blog.
So what can you do to keep your data private and secure?
Opt Out of iCloud Backups
iOS devices encrypt all their data, including your (DEVONthink To Go databases, and we still have no reason to believe that there’s a back door. What is on your locked devices stays locked away even when your devices fall into the hands of other people. But while your devices uploaded encrypted backups to iCloud, Apple has a second key for them. So technically they are an open book.
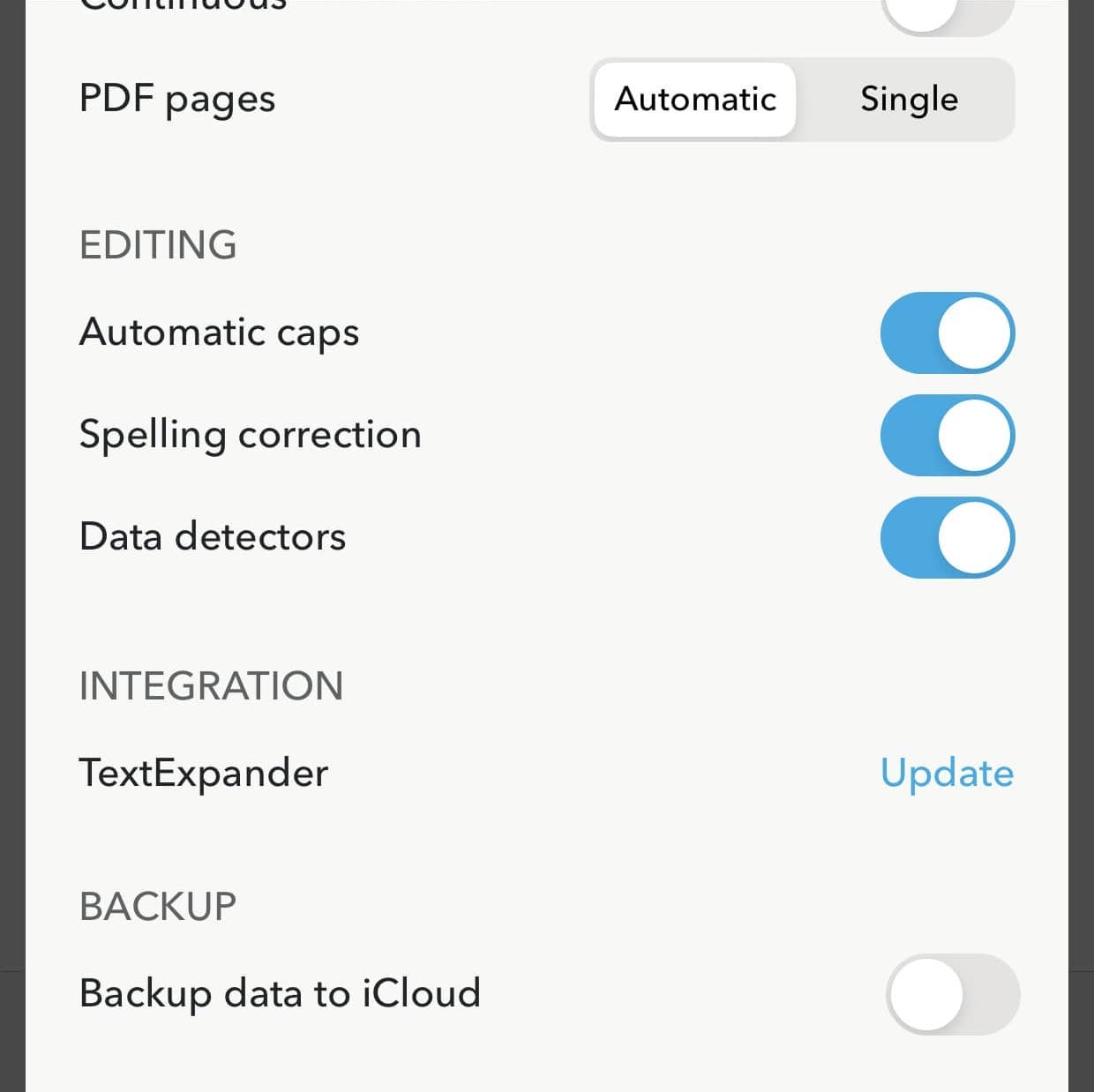
You can opt out of all iCloud backups in iOS’ Settings and manually backup your device with iTunes (before macOS Catalina) or the Finder. Alternatively, DEVONthink To Go gives you the option to keep just your databases out of the iCloud backup. Visit the app’s Settings, scroll all the way down, and check the Backup data to iCloud switch. Switch if off if you don’t want iOS to upload your data to iCloud.
Encrypt Your Sync Stores
Regardless what service you use for synchronizing your data we recommend that you encrypt your sync store. When setting up the sync store you have the option to enter an encryption key. DEVONthink uses this to encrypt your data using AES-256 before uploading.
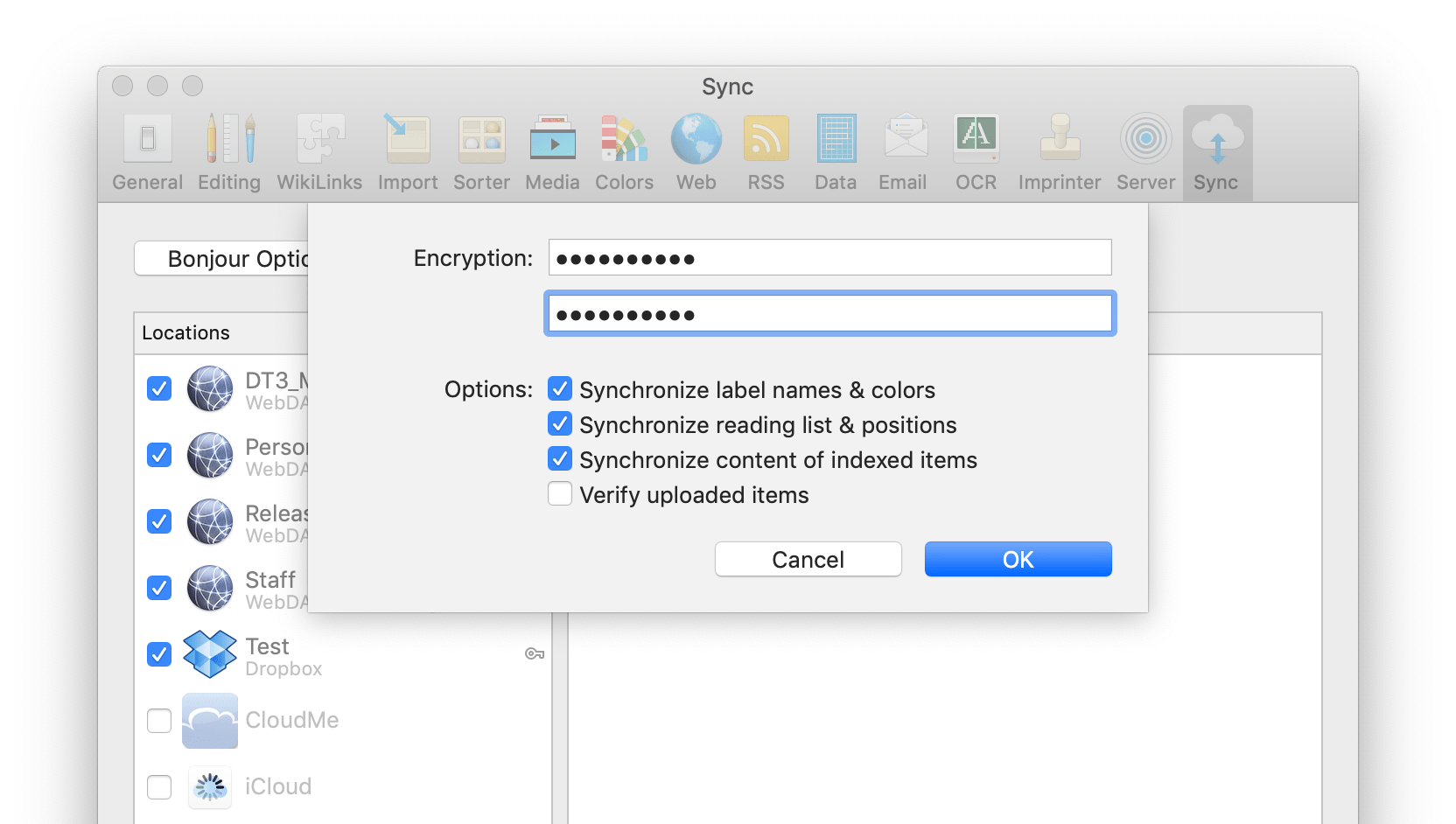
You can safely use potentially compromised locations like iCloud, Dropbox, or WebDAV services for synchronizing your data. All files DEVONthink puts on the servers are useless without the correct key. And there is no back door.
If you add an encryption key to an already existing, not encrypted sync store you’ll be asked to empty the sync store and re-upload your data. On iOS you must make sure that you’ve downloaded all documents before you do this, e.g., by switching the sync location to Download: Always.
Turn on File Vault
macOS can encrypt your Mac’s hard drive with FileVault which also uses AES. If you want to make sure that someone who gets his hands on your computer cannot access your data, you should switch this on. Without your encryption key (password) it will no longer be possible to use your Mac or read your files.
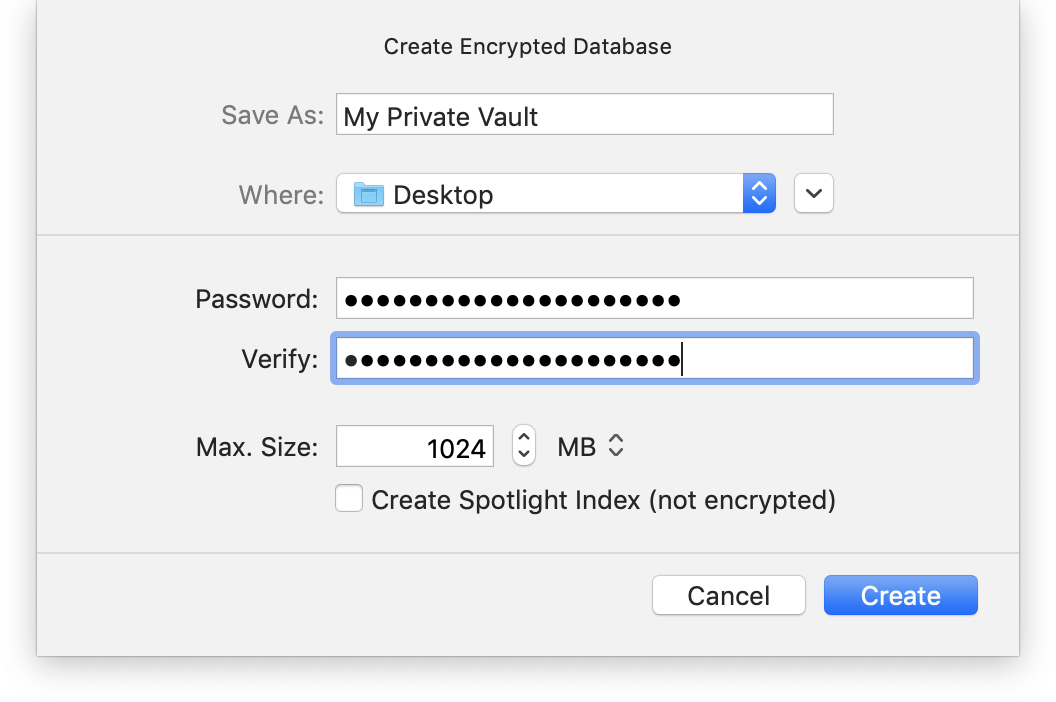
Use Encrypted Databases
For extra security we recommend to store private data in encrypted DEVONthink databases. If you cannot or do not want to keep them in a database, encrypted disk images are a good alternative. They are, again, based on AES encryption and are actually used by DEVONthink for its encrypted databases too. You create them with the Disk Utility app.
DEVONthink To Go does not encrypt the data on disk as iOS devices are encrypted by default. As of this writing we still trust Apple here. But if you leave your devices behind unlocked, anyone could open the app and have a look at your data. If you worry, set a passcode and activate Face ID or Touch ID in Settings > Security.
Encrypt Your Backups
Finally, your backups can be a weak point. If you encrypt your DEVONthink databases or store files in encrypted disk images they’ll be safe in your backups, too. But your other files may not. Time Machine uses AES to encrypt your backups and so can almost any third-party backup software we know. We tend to name Arq when someone asks but there are many others.
Keep Your Encryption Keys Safe
If everything is nicely encrypted, from your Mac and iOS devices to your databases and your backups, you must make sure that you know the encryption keys that you used.
One possible reason why Apple keeps copies of iCloud backup keys might be that they can use them to help customers who no longer know their keys. Encrypted DEVONthink databases, sync stores, disk images, and Time Machine backups are different. If you lose the encryption keys for them there is no way to get access, neither for Apple nor for us. If we could break in then anyone could.
